The North Korean attacker gang known as ‘BlueNoroff’ has been addressed the targeting cryptocurrency startups with malicious documents and fake MetaMask browser extensions.
The main motive of the gang is purely financial, but its sophistication in carrying out the objective has priory led investigators to conclude that this is a sub-group of the North Korean Lazarus group.
Although BlueNoroff has been active for several years, its structure and operation have been shrouded by mystery. A report by Xiarch researchers attempts to shed some light by using intelligence collected during the most recent activity observed, dating back to November 2021.
What are its Targets?
The latest attacks are focused on cryptocurrency startups located in the US, Russia, China, India, the UK, Ukraine, Poland, Czech Republic, UAE, Singapore, Estonia, Vietnam, Malta, Germany, and Hong Kong.

The threat actors attempt to infiltrate the communications of these firms and map the interactions between the employees to derive potential social engineering pathways. In some cases, they do this by compromising the LinkedIn account of an employee and sharing a link to download a macro-laced document right on the platform.
BlueNoroff uses these real discussions to name laced documents accordingly and send them to the target employee at the right time.
To track their campaign, they include an icon from a third-party tracking service (Sendgrid) to get a notification when the victim opens the sent document. The company names and logos impersonated by BlueNoroff are shown below:

At Xiarch, these organizations may not have been negotiated, and Sendgrid may not know was alerted that North Korean APTs are harming them.
What are the Condition chains?
The first infection chain uses documents that feature VBS scripts, which exploit an old remote template injection vulnerability (CVE-2017-0199).
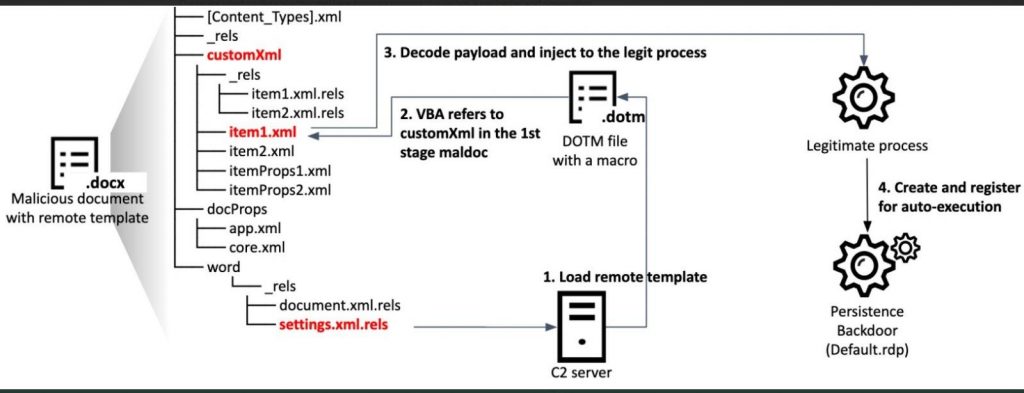
The second infection chain relies on sending an archive that contains a shortcut file and a password-protected document (Excel, Word, or PDF).
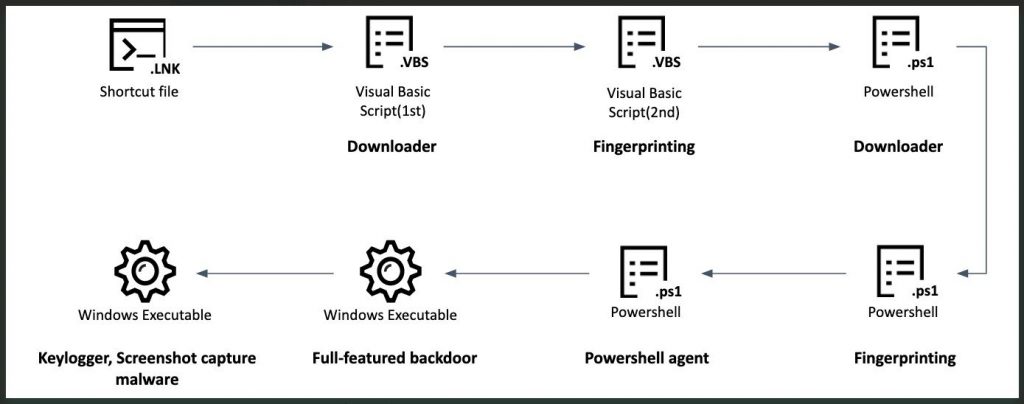
The LNK file that supposedly contains the password to open the document initiates a series of scripts that fetches the next-stage payload. Eventually, in both cases, a backdoor with the subsequent functionalities is dropped onto the infected machine:
- Directory/File manipulation
- Process manipulation
- Registry manipulation
- Executing commands
- Updating configuration
- Stealing stored data from Chrome, Putty, and WinSCP
Fake MetaMask steal crypto from victims
BlueNoroff steals user credentials that can be used for lateral movement and deeper network infiltration, while they also collect configuration files relevant to cryptocurrency software.
“In some cases where the attackers realized they had found a prominent target, they carefully monitored the user for weeks or months,” reads Xiarch report. “They collected keystrokes and monitored the user’s daily operations while planning a strategy for financial theft.”
The main trick employed to steal the cryptocurrency investments is to return the core elements of wallet management browser extensions with tampered versions that are dropped on local memory.
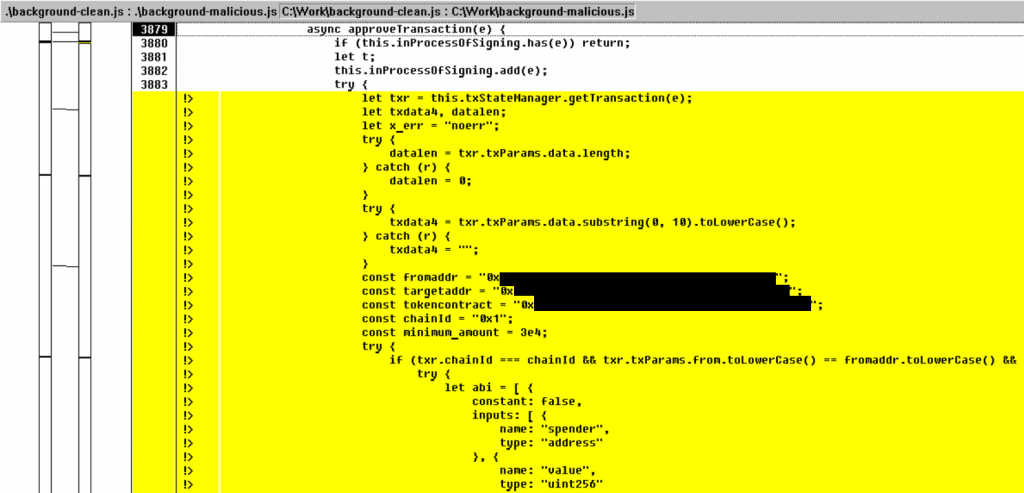
Xiarch notes that tampering with the Metamask Chrome extension requires a thorough analysis of 170,000 lines of code, indicative of the skills and determination of BlueNoroff.
Victims can only detect the extension is fake by switching the browser to Developer mode and seeing the extension source pointing to a local directory rather than the online store.
When the target uses a hardware wallet, the actors wait for marketings and seize the quantities by changing the recipient’s address. Because they have only one possibility before the target acknowledges the infection, the actors also change the transaction amount to the maximum possible, draining the assets in one move.
Indications for attribution
On the element of attribution, Xiarch researchers convey seeing overlappings and parallels between PowerShell scripts and backdoors operated in the most delinquent and past movements.
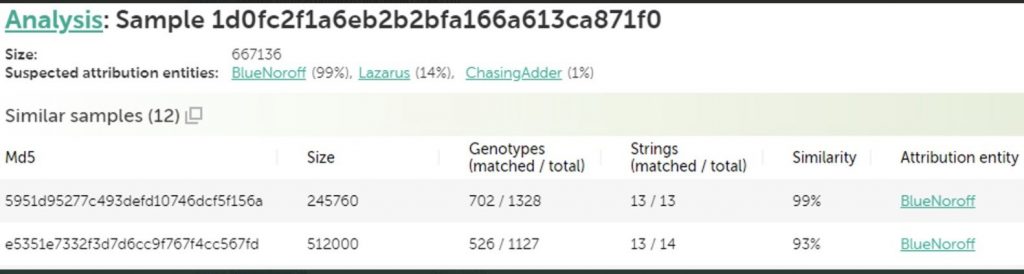
Moreover, the C2 address acquisition method is identical to the 2016 attacks, using a hardcoded DWORD matter to select an IP address through XORing. Ultimately, the metadata on the Windows shortcut files settled as part of the dual infection chain containing Korean characters.



