AvosLocker is the latest ransomware gang that has added support for encrypting Linux systems to its recent malware variants, specifically targeting VMware ESXi virtual machines. While we couldn’t find what targets were attacked using this AvosLocker ransomware Linux variant, Xiarch knows of at least one victim that got hit with a $1 million ransom request.
A few months ago, the Avos Locker group was also seen promoting its latest ransomware variants, the Windows Avos2 and Avos Linux, while making a point of warning affiliates not to attack post-soviet/CIS targets.
“Out new modification like avos2 or avoslinux have the best of both worlds to offer: high performance & high amount of encryption related to its applicants,” the group said.
ESXi VMs Terminated before Encryption
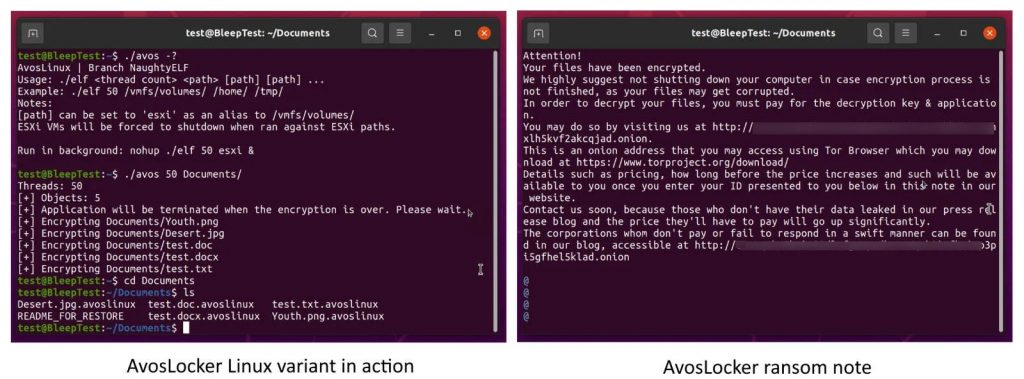
Once started on a Linux system, AvosLocker will terminate all ESXi machines on the server utilizing the following command:
esxcli –formatter=csv –format-param=fields==”WorldID,DisplayName” vm process list | tail -n +2 | awk -F $’,’ ‘{system(“esxcli vm process kill –type=force –world-id=” $1)}’
Once it starts operating on a compromised system, the ransomware will append the .avoslinux extension to all encrypted files.
A safety researcher told our experts that AvosLocker began using the Linux encryptor starting in November 2021.
Why did Ransomware switch to Linux?
Avos Locker is a more recent gang that first materialized during the summer of 2021, reaching for ransomware companions on underground forums to join their newly launched Ransomware-as-a-Service (RaaS) operation. The movement to target ESXi virtual appliances aligns with their enterprise targets, who have recently emigrated to virtual machines for easier device management and more efficient help use.
By targeting the VMs, the ransomware operators also take benefit of easier and faster encryption of multiple servers with a single command. Since October, Hive ransomware started encrypting Linux and FreeBSD systems using new malware variants, within months after researchers spotted a REvil ransomware Linux encryptor targeting VMware ESXi VMs.
Emsisoft CTO Fabian Wosar told Xiarch that other ransomware gangs, including Babuk, RansomExx/Defray, Mespinoza, GoGoogle, DarkSide, and Hellokitty, have also created and used their own Linux encryptors. “The explanation why most ransomware groups implemented a Linux-based version of their ransomware is to target ESXi specifically,” Wosar explained.
HelloKitty and BlackMatter ransomware Linux variants were also found in the wild by security researchers in July and August, further confirming Wosar’s statement. The Snatch and PureLocker ransomware operations have also been observed utilizing Linux encryptors in the past. You can find more info on AvosLocker ransomware and what to do if you get plugged by this ransomware family in our support topic.



