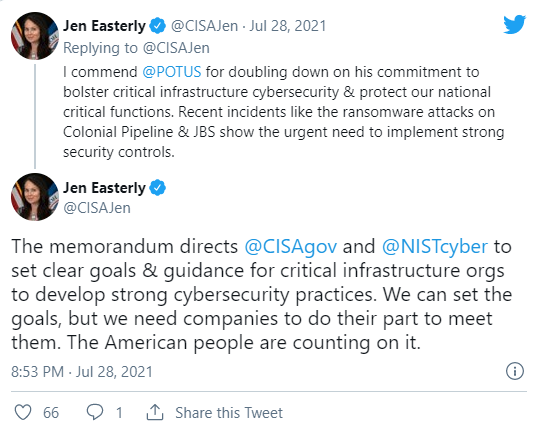
Joe Biden US President today issued a national security memorandum designed to help in enhancing the security of critical infrastructure by setting baseline performance goals for critical infrastructure owners and operators. The memorandum arrives a revert to recent attacks across the world which includes ransomware attacks on Colonial Pipeline and JBS Foods in the United States that discovered some vulnerabilities across US infrastructure, largely owned and operated by private sector orgs.
It directs the Department of Homeland Security’s CISA and the Department of Commerce’s NIST, as combined with other federal agencies, to develop cybersecurity performance aims and guidance for sensitive frameworks orgs. “We expect those standards will guide companies and responsible for giving important services like water, power and transportation to enhance their cybersecurity,” a White House statement said.
“Responsible sensitive frameworks owners and operators should be following voluntary guidance as well as important needs in order to make sure that the sensitive services the American people rely on are secured from the cyber threats,” a senior administration official added.
Private Sector Urged to Join Federal Government’s Efforts
Today’s NSM also makes the President’s Industrial Control System Cybersecurity (ICS) Initiative, a voluntary, combinative effort between the sensitive framework community and the federal government started in the mid of April to provide the set up of technology providing threat visibility, indicators, detections, and alerts.
The ICS initiative has already led to over 150 electricity aspects which represent roughly 90 million customers set up or agreeing to set up control system cybersecurity technologies in the future.
“These are the technologies that, had they been in place, would have blocked what occurred at Colonial Pipeline in that they connect the operational technology side of the network to the IT side of the network,” a senior administration official further explained. “These action plans for natural gas pipelines is underway, and additional initiatives for other sectors will pursue later this year.”
The private sector (which includes all responsible critical framework owners and operators) is urged to approve the new goals and guidance CISA and NIST will outline as part of a shared effort to protect the USA’s sensitive framework.
This National Security Memorandum, the ICS Cybersecurity Initiative, TSA’s Security Directives, and foundationally, the President’s Executive Order on Improving the Nation’s Cybersecurity that he signed back in May all are parts of our focused and aggressive continuing effort to address these significant threats to our nation within that first line of modernizing defense of our cybersecurity — of the administration’s cybersecurity strategy. — Senior Biden administration official
Severe Security Breaches Could Lead to Real War
Yesterday, President Joe Biden alerted that Cyberattacks leading to severe security breaches could lead to a “real shooting war” with another major world power.
“You know, we have seen how cyber threats, consisting ransomware attacks, progressively are able to cause damage and disruption to the real world,” Biden stated during a speech at the National Counterterrorism Center of the Office of the Director of National Intelligence.
“I can’t ensure this, and you are informed as I am, but I thinks it’s more likely we are going to end up –well if we end up in a war, a real shooting war with major power, it is going to be as a consequences of a cyber breach of great consequences.”
Biden’s also remarks come after a NATO statement from the mid of June that compare the impact of “significant” Cyberattacks to ‘armed attacks.’ “We continue that a decision as to when a cyber attack would lead to the appeal of Article would take by the North Atlantic Council on a case-by-case basis,” the NATO spokesperson said.
“Some of the allies recognize that the impact of significant malicious malware aggregate Cyber activities may, in some of the circumatnces, be taken as amounting to an armed attack.”