New NPM Trojan has been discovered hijacking credentials from the Google Chrome web browser by using appropriate password recovery tools on Windows systems.
Moreover, this Trojan observes for incoming connections from the threat actor’s C2 server and gives new functionalities, such as screen and camera access, file lookup, shell command execution, file upload, and directory listing.
As discovered by our experts, the identified packages have been sitting on the NPM registry since 2018 and scored over 2,000 totals downloads at the time of writing.
Use ChromePass utility to ‘recover’ Chrome Passwords
Today, Investigators at ReversingLabs have revealed their researches on two malicious npm packages that secretly hijack credentials from your Chrome web browser.
These packages are called:
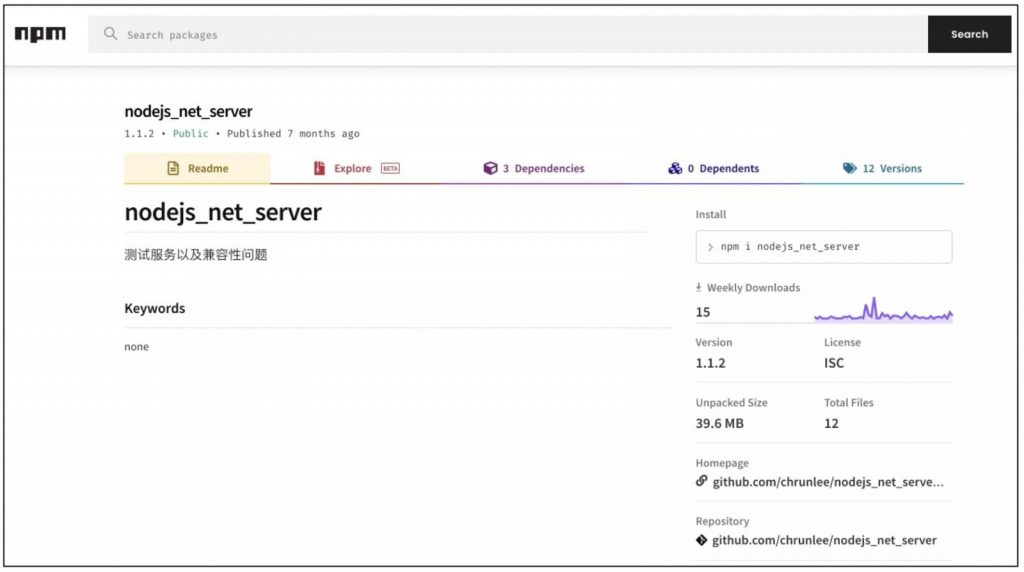
- nodejs_net_server – over 1,300 total number of downloads
- temptesttempfile – over 800 total downloads
These packages were found by ReversingLabs Titanium Platform static analysis engine that employed machine learning algorithms.
But the main focus of the reports is on nodejs_net_server which contains the core malware features.
The Trojan targets Windows machines to hijack user passwords and also sets up a persistent remote backdoor for the threat actors to conduct surveillance activities.
To provides its credential-stealing activities, the Trojan specifically “nodejs_net_server,” uses the appropriate ChromePass freeware facilities for Windows. ChromePass is one of the password recovery tools for Windows systems that major goal is to extract credentials from the user’s Chrome web browser:
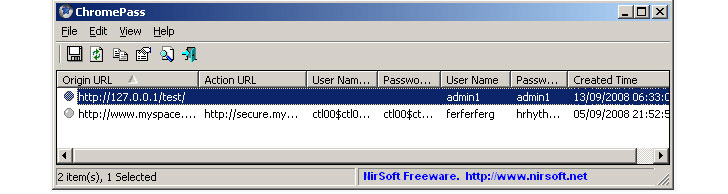
The utility is packed inside the npm package with cryptic or misleading names, like a.exe.
Disregarding, as ChromePass executables have previously been flagged by VirusTotal as malicious.
The “nodejs_net_server” has had 12 versions published to date, with the advanced on 1.1.2 computing about 40 MB in size uncompressed.
In later versions, though, the Trojan is seen launching TeamViewer.exe to bypass raising red flags.
Harm NPM Configuration options to Gain Perseverance
Most malicious npm packages caught thus far rely on typosquatting or dependency confusion to infect developers. But that is not the case with these packages, and it’s not yet been discovered that how these packages handle get so many downloads.
We haven’t discovered any obvious typosquatting target by examining the package name. It is still unclear to us how the author aimed to manipulate users into installing the package. We can however see download activity on the packages statics page.
We have contacted NPM to take the package down. We are still waiting on their security team to respond, “ReversingLabs” chief software architect and co-founder, Tomislav Pericin told our experts in an email interview.
“We removed the package in accordance with npm’s acceptable use policy regarding malware, as mentioned in its Open-Source Terms,” a GitHub spokesperson told our experts.
Interestingly, as soon as the package is installed by the developer, it attempts to gain endurance on the Windows machine by harming the well-known npm configuration option, “bin”.
The “bin” option in the package’s manifest file, package’s manifest file, package.json, is proposed at stealing the popular “jstest” package, should it be pre-installed on a developer’s machine.
“jstest” is a cross-platform JavaScript testing infrastructure downloaded over 36,000 times to date – meaning, high chances a NodeJS developer would have it.
Whoops! The trojan author reveals their Passwords
In an unexpected twist, some versions of nodejs_net_server contain text files with usernames and plaintext credentials of the Trojan author, separated from Chrome.
ReversingLabs consider this to be an incident on the author’s part:
“One of the funniest facts related to versions that accommodate the password recovery tool is that the package author accidentally published their own, preserved login credentials.”
“It comes that the posted versions 1.1.1 and 1.1.2 from the NOM repository include the results of testing the ChromePass tool on the author’s personal system.”
“These login credentials were stored in the ‘a.txt’ file located in the same folder as the password recovery tool named as ‘a.exe’,” told by ReversingLabs reverse engineer Karlo Zanki.
Over the last few months, attacks on open source ecosystems including, npm, PyPI and RubyGems have grown regularly.
While the recent reports of current dependency stealing attacks flooding open source repos, the main concern is not going away anytime soon.
“We are still to see a malicious repository package enclose itself in the final release image, but that seems like it’s only a matter of time with the current state of things,” concluded Pericin.



