The Cybersecurity & Infrastructure Security Agency, CISA alerts of threat actors targeting “a well-known, previously patched, vulnerability” discovered in SonicWall Secure Mobile Access (SMA) 100 series and Secure Remote Access (SRA) products with end-of-life firmware. As the US federal agency also stated, that the threat actors are able to exploit the security vulnerability as part of a target ransomware attack.
This warning comes after SonicWall issued an “immediate security notice” and transmit emails to alert the customers of the “immediate risk of a targeted ransomware attack.” Even though the organization said the risk of ransomware attacks is imminent, Coveware CEO Bill Segal proved CISA’s warning saying that the operation is in process.
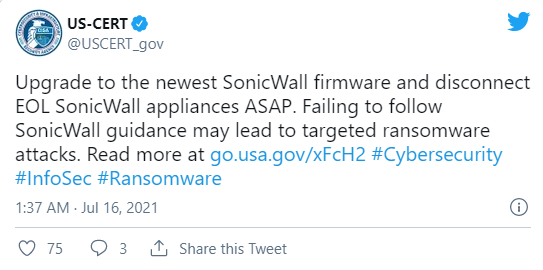
CISA urges users and administrators to go through the SonicWall security notice and upgrade their devices to the latest firmware or instantly disconnect all end-of-life tools.
One of the Groups is behind these Attacks – HelloKitty Ransomware
While CISA and SonicWall did not disclose the identity of the threat attackers behind these attacks, our investigators got to know by a source in the cybersecurity industry that HelloKitty has been exploiting the vulnerability for some previous weeks.
Cybersecurity association CrowdStrike also proved that the recent attacks are attributing to multiple threat actors, including HelloKitty. HelloKitty is a human-operated ransomware operation active since November 2020, mostly known for encoding the systems of CD Projekt Red and asserting to have hijacked Cyberpunk 2077, Witcher 3, Gwent, and other game’s source code.
Although the weakness harmed to negotiate unpatched and EOL SMA and SRA products were not revealed in CISA’s warning or SonicWall’s notice, CrowdStrike security investigator Heather Smith told our experts that the targeted vulnerability is tracked as CVE-2019-7481.
“This exploitation targets a well-known vulnerability that was patched in advanced versions of firmware released in early 2021,” SonicWall said in an emailed statement. However, CrowdStrike’s Heather Smith and Hanno Heinrichs said in a report posted last month that “CrowdStrike Services incident response teams identified eCrime actors leveraging an older SonicWall VPN vulnerability, CVE-2019-7481, that impacts Secure Remote Access (SRA) 4600 devices.”
SonicWall recently created two securities with reporting the actively exploited security flaw in a security advisory concerned yesterday. As per as Coveware report, Babuk ransomware is also targeting SonicWall VPNs likely vulnerable to CVE-2020-5135 exploits. This vulnerability was patched in October 2020 but it is still “heavily harmed by ransomware gangs today” per Coverware.
Ransomware vs. SonicWall devices
A group of the attacker by Mandiant as UNC2447 has also exploited the CVE-2021-2016 zero-day bug in SonicWall SMA 100 Series VPN appliances to set up a new ransomware strain known as Fivehands. Their attack targeted numerous North American and European targets before SonicWall released patches in late February 2021.
A similar zero-day was also harmed in January in attacks targeting SonicWall’s internal systems and later instinctively exploited in the wild. Mandiant threat assessment discovered three other zero-day vulnerabilities in SonicWall’s on-premises and hosted Email Security (ES) products in March.
All the three zero-days were also currently exploited by a group Mandiant tracks as UNC2682 to backdoor systems using BEHINDER web shells, permitting them to transmit laterally through the victim’s network and access emails and files.
“The adversary leveraged these vulnerabilities, with confidential knowledge of the SonicWall application, to install a backdoor, access files and emails, and move laterally into the victim organization’s network.”



