A joint security advisory concern discovered today by some cybersecurity agencies from the US, the UK, and Australia reveals the top 30 most targeted security vulnerabilities of the last two years. CISA, the Australian Cyber Security Center (ACSC), the United Kingdom’s National Cyber Security Center (NCSC), and the Federal Bureau of Investigation (FBI) also shared mitigation to help private and public sector organizations counter these vulnerabilities.
“Collaboration is a most crucial part of CISA’s work and today we collaborate with ACSC, NCSC and FBI to highlight cyber vulnerabilities that public and private organization should prioritize for patching to minimize risk of being exploited by malicious actors,” said Eric Goldstein, CISA Executive Assistant Director for Cybersecurity.
Attacks Focused Remote Work, VPN, Cloud Technologies
Based on information gathered by the US Government, most of the top targeted errors last year were revealed since the start of 2020, with the trend stemming from the recent move to remote work since the starting of the pandemic.
“The immediate shift and increased use of remote work options, such as Virtual Private Networks (VPNs) and cloud-based surroundings, likely placed additional force on cyber defenders suffering to handle and keep pace with routing software patching,” CISA explains.
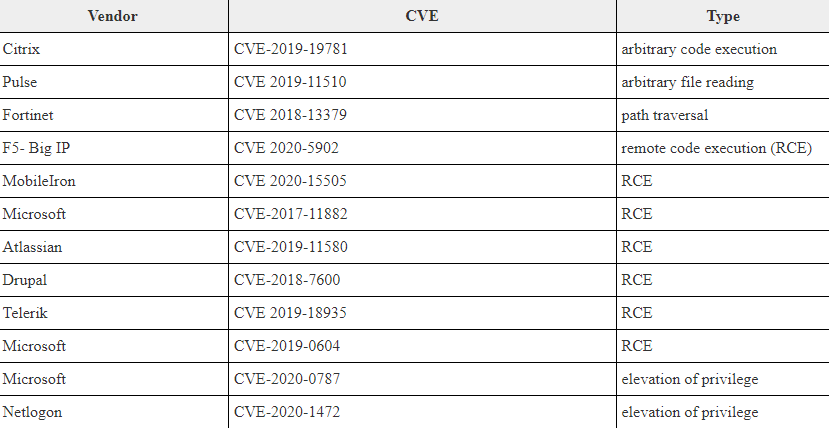
While the attackers are taking advantage of the situation to remote working, four of the most constantly targeted vulnerabilities during 2020 harm work-from-home (WFH), VPNs, or cloud-based technologies, as mentioned in the table below.
“In 2021, malicious cyber actors constant to target various vulnerabilities in perimeter-type devices. Among those very highly exploited in 2021 are vulnerabilities in Microsoft, Pulse, Accellion, VMware, and Fortinet,” CISA stated. As further mentioned in the advisory, attackers keep exploiting publicly called (often old) security flaws harming a broad set of targets from various industry sectors.
Why did Companies urge to Patch their System?
CISA, ACSC, the NCSC, and the FBI advise public and private orgs across the world to patch and update their systems as soon as possible to reduce their attack surface.
“Individuals across the world can mitigate the vulnerabilities listed in this report by implementing the available patches to their systems and implementing a centralized patch management system,” the joint advisory stated. Those who cannot urgently patch or don’t plan to patch soon should go through for signs of negotiation and initiate incident response at a time and recovery plans.
The four agencies have also revealed indicators of negotiation, recommended mitigations, various detection methods, and links to patches for each of the vulnerabilities listed in the advisory. “The advisory posted today puts the power in each and every association’s hand to fix the most common vulnerabilities, like unpactched VPN gateway devices,” NCSC’s Director for Operation, Paul Chichester added.
“Working with the international partners, we will promote to raise awareness of the threats posed by those that seek to cause a big harm.”