The United States government has taken two major active actions to fight and defend malicious cyber activities affecting the country’s business and sensitive framework sectors.
One action is a website with resources from across the federal government created to help businesses and communities from ransomware attacks.
The other one is by gifting a reward of up to $10 million for any information on operations conducted by threat actors working for a foreign government.
How do they deal with Ransomware Threats?
In early this week, the U.S. Government started the StopRansomware.gov website especially to help private and public entities mitigate the ransomware threat.
It is means as a central platform for data about ransomware collected from all the federal government agencies, which consists up of the instructions, the latest alerts, resources, and all the updates.
From the U.S. Department of Homeland Security, “StopRansomware.gov includes resources and content form DHS’s Cybersecurity and Infrastructure Security Agency (CISA) and the U.S. Secret Service, the Department of Justice’s Federal Bureau of Investigation (FBI). The Department of Commerce’s National Institute of Standards and Technology (NIST), and the Departments of the Treasury and Health and Human Service.”
The ransomware threat has increased to extraordinary levels lately, with attacks on critical frameworks and businesses that break into the regular individual.
Cyberattacks on giants like JBS Foods, one of the largest meat producers in the world, on Colonial Pipeline – the main fuel supply line for the U.S East Coast, or the most recent one on Kaseya, which affected up to 1,500 businesses worldwide, highlighted, even more, the effort important to handle it.
Following Nation-State Hackers
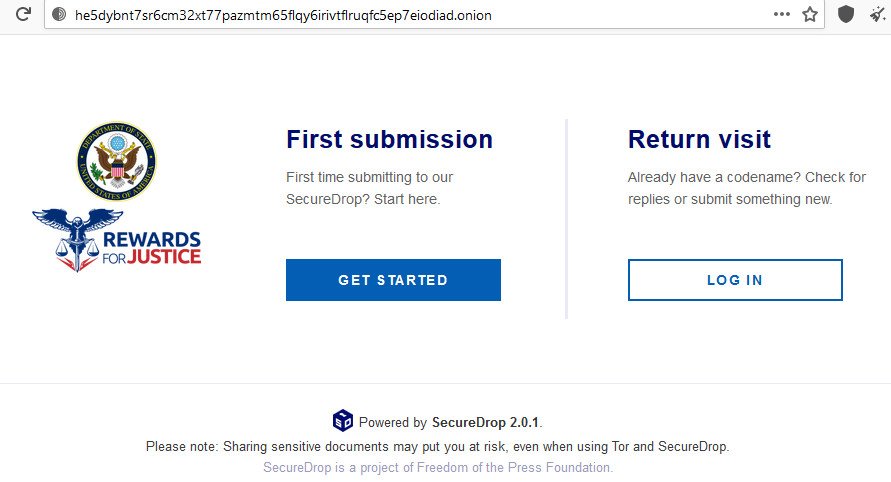
On Thursday, the U.S. Department of State announced that its Rewards for Justice (REJ) program now encouraging reports of foreign malicious activity against U.S. sensitive infrastructure.
The price is up to $million and it is designed for details that can help discover and locate any person that acts on behalf of a foreign government in a malicious cyber operation.
The actions may include fraud as part of a ransomware attack, hijacking data from protected systems, “and consciously causing the communication of a program, data, code, or command, and as a result of such conduct, intentionally causing damage without authorization to a protected computer.”
“Secured computers include not only U.S. government and financial institution computer system, but also those used in or affecting interstate or foreign commerce or communication,” by U.S. Department of State
The payment may be enough to encourage hackers involved in attacks affecting critical infrastructure in the U.S. to turn on each other and get a legal, stress-free payout.
To get the data in a protected design and to protect the safety of probable sources, the Department of State set up a tips-reporting service on the dark web:
http://he5dybnt7sr6cm32xt77pazmtm65flqy6irivtflruqfc5ep7eiodiad.onion [access through Tor browser]
For this intention, REJ is using the SecureDrop platform that is used by researchers for protected communication with their sources and to secure their identity by using random codes instead of a username.
Moreover, payments through the REJ program may also be in cryptocurrency, which can help tipsters maintain their anonymity and receive and reward.
The REJ program started in 1948 and has paid more than $200 million to over 100 individuals offering data that helped in the fight against terrorism (prevent terrorist acts, bring terrorists to justice) and deal with threats against U.S. national security.



