Cloudflare has fixed a critical vulnerability in its free and open-source CDNJS probably impacting 12.7% of all the websites on the internet. CDNJS deliver million of websites with over 4,000 JavaScript and CSS libraries preserved publicly on GitHub, creating it the second-largest JavaScript CDN.
The vulnerability exploits negotiate publishing packages to Cloudflare’s CDNJS using GitHub and npm, to trigger a Path Traversal vulnerability, and eventually remote code execution. In case exploited, the vulnerability would lead to complete negotiation of CDNJS infrastructures.
From “ZIP Slip” to remote code execution
This week, security researcher Ryotak explains how he was able to find a method to completely negotiate Cloudflare’s CDJNS network while researching supply-chain attacks. Content delivery networks (CDNs) executes a critical role in maintaining the security, availability of the Internet as a broad majority of websites rely on these services to load popular JavaScript libraries and CSS scripts.
CDNs can become a choice of targets for adversaries as, if compromised, the attack can have far-reaching limitations for many websites, online stores, and their customers. While glancing over cdnjs.com, RyotaK noticed that for libraries that did not yet exist in CDNJS, he could advise the addition of a new library via the CDNJS GitHub repository.
After going through this GitHub repository and the adjacent ones that together make the CDNJS ecosystem work, Ryotak finds a way to trick the servers into running the arbitrary code. Particularly, the investigator studied the scripts present in cdjns/bot-ansible and cdjns/tools, including an auto-update script that provides automatic retrieval of library updates.
These scripts would periodically update the CDJNS server with newer versions of software libraries released by their authors on the corresponding npm registry.
In other words, for every library published to CDNJS GitHub repo, its updated version would be downloaded from the linked npm registry, with the npm version also managed by the library author. Ryotak wondered what would appear if a library he had published to CDNJS had its corresponding npm version containing a Path Traversal exploit. Note, npm packages are published as TGZ (.tar.gz) archives which can easily be crafted with path traversal exploits hiding within.
The investigator first published to npm, which would eventually get processed by CDJNS updates bots, the researcher inserted Bash scripts in strange-looking ways, These different ways are nothing other than Path Traversal exploits hidden inside ZIP/TGZ archives, a concept well-known in 2018 as “ZIP Slip.”
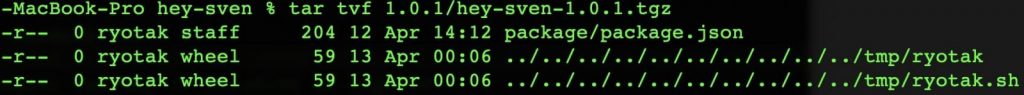
Once CDNJS servers processed the crafted “hey-sven” npm archives, the data of these Bash scripts would be run on the server. But, the investigator did not want to mistakenly overwrite an existing script so he first utilized a symlink vulnerability to go through the data of the files he was about to overwrite, during the proof-of-concept (PoC) test.
“As Git supports symbolic links by default, it may be possible to read arbitrary files from the cdjns library update server by adding symlink into the Git repository.”
“If the constantly executed script file is overwritten to run arbitrary commands, the automatic update process may be crashed, so I decided to go through the arbitrary file,” the researcher said.
As soon as his crafted PoC hit the server, Ryotak was able to suddenly dump sensitive secrets such as GITHUB_REPO_API_KEY and WORKERS_KV_API_TOKEN into scripts served by the CDN at https://cdjns.clodflare.com/…

Cloudflare Concerns many Fixes to Extinguish the Bug
The investigator reported this vulnerability to Cloudflare via HackerOne’s vulnerability disclosure program on April 6th, 2021, and saw Cloudflare’s team applying a periodic fix within hours.
The initial fix seen by our experts is indented at resolving the symlink vulnerability:
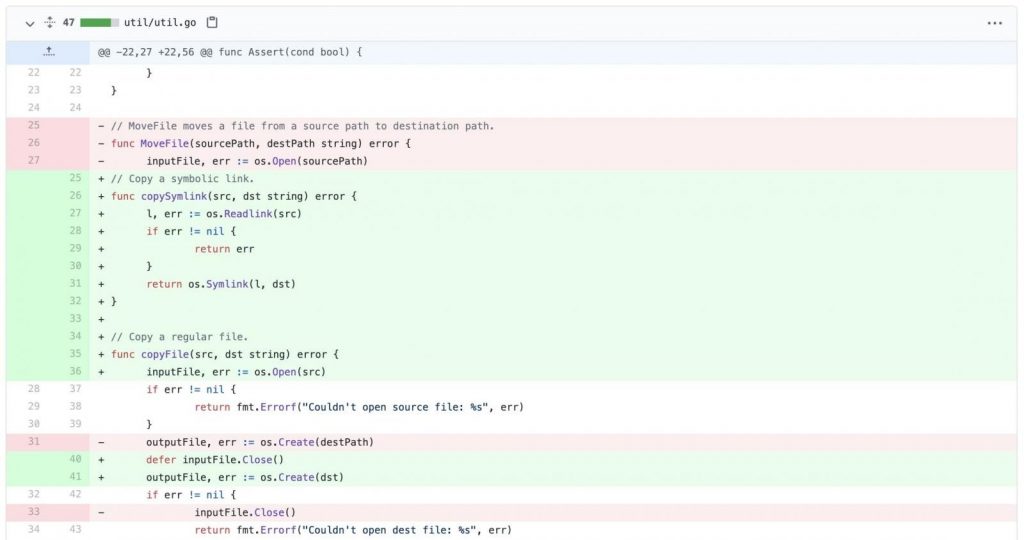
Although, due to the tediousness of the CDNJS ecosystem, a series of more concrete fixes were applied over the following weeks to various repositories according to the researchers. RyotaK shared with our experts that while the initial fix was centered around denying symbolic links (symlinks) in Git repositories, it only mitigate a part of the problem.
“They tried to neglect symlinks first, but they noticed that current design of the bot is too harmful. So they isolated most harmful feature.” “And for other features, they apply AppArmors,” the investigator said. Application Armor is a security process that mitigates the capabilities of programs running on Unix-based environments with predefined profiles so that the programs don’t recklessly exceed their aimed scope of access.



