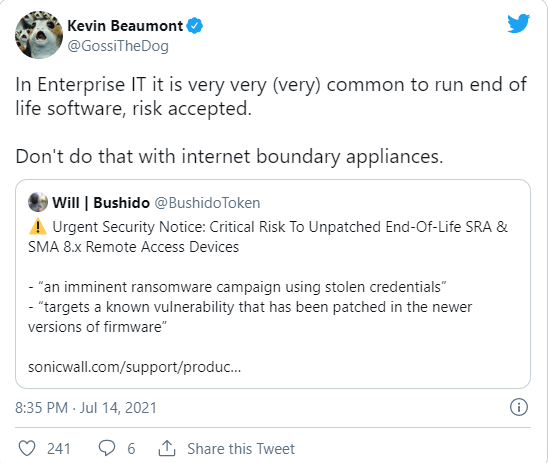
SonicWall has concerned an “urgent security notice” warning customers of ransomware attacks targeting unpatched end-to-life (EoL) Secure Mobile Access (SMA) 100 series and Secure Remote Access (SRA) products.
The company said that “Through the course of collaboration with trusted third parties, SonicWall has been get to know about threat actors currently targeting Secure Mobile Access (SRA) products running unpatched and end-of-life (EOL) 8.x firmware in an imminent ransomware operation by utilizing hijacked information.”
According to SonicWall, the attacks target a well-known vulnerability addressed in the advanced version of firmware, and they do not impact SMA 1000 series products.
“Companies that are unable to take right actions to avoid these vulnerabilities on their SRA and SMA 100 series products are at potential risk of a targeted ransomware attack.” SonicWall alerts.
What to do With the Affected Devices?
Organizations still using EoL SMA and/or SRA devices with 8.x firmware are requested to update the firmware urgently or disconnect the tools as soon as possible to protect from the critical risk of ransomware attacks.
Customers using recent supported SMA 210/410/500v devices with the vulnerable 8.x firmware targeted in these attacks are also suggested to urgently update to the latest version, which bypasses vulnerabilities discovered in early 2021.
“According to the additional mitigation, you should also urgently reset the id passwords relate with your SMA or SRA device, as well as any other system or devices by utilizing the similar credentials,” SonicWall said. “As always, we potentially recommend enabling multifactor authentication MFA).”
Depending on the product they use, SonicWall suggests organization to:
- SRA 4600/1600 (EOL 2019)Disconnect immediately
- Reset Passwords
- SRA 4200/1200 (EOL 2016)
- Disconnect immediately
- Reset Passwords
- SSL-VPN 200/2000/400 (EOL 2013/2014)
- Disconnect immediately
- Reset Passwords
- SMA 400/200 (Still Supported, in Limited Retirement Mode)
- Update to 10.2.0.7-34 or 9.0.0.10 immediately
- Reset Passwords
- Enable MFA
SonicWall also shared the below statement with our experts relating the attacks:
“Attackers will take any opportunity to exploit organizations for malicious access. This exploitation directly targets a well-known vulnerability that was patched in newer version of firmware released in early 2021. SonicWall urgently and frequently contacted to the affected organizations of reduction steps and update guidance.”
Even though the footprint of affected or unpatched devices is relatively small, SonicWall constantly strongly advises organizations to patch supported devices or deactivated security tools that are no longer supported, especially as it gets advanced intelligence about appearing threats. The constant uses of unpatched firmware or end-of-life devices, disregarding of the vendor, is an active security risk.”
SonicWall Gadgets already targeted by Ransomware
In April, Attacker also abused a zero-day bug in SonicWall SMA 100 Series VPN tools to set up a new ransomware strain called FiveHands on the networks of North American and European targets.
This threat gang, tracked by Mandiant as UNC2447, exploited the CVE-2021-20016 SonicWall vulnerability to hijack the device and transmit FiveHands ransomware payloads before Sonicwall released patches in the last of February 2021.
The same zero-day was also harmed in attacks targeting SonicWall’s internal systems in January and later exploited instinctively in the wild.
In March, Mandiant threat assessment found three more zero-day vulnerabilities in SonicWall’s on-premises and hosted Email Security (ES) products.
These zero-day were also currently exploited by a group tracked as UNC2682 to backdoor systems using BEHINDER web shells, permitting them to move alongside through the victim’s network and achieve access to crucial emails and sensitive files.



